How to Read a Pnpdevice as an Object Powershell
Passing through devices to Hyper-V VMs by using discrete device assignment
![]()
Dr Scripto
Summary: Learn how to attach a device from your Hyper-5 host to your VM by using a new characteristic of Windows Server 2016.
Today we have a guest blogger, Rudolf Vesely, who has blogged here on previous occasions. Hither is a link to his previous posts if yous would like to read them.
Here is what Rudolf says almost himself.
I am an Azure Solutions Architect at Rackspace in London. I believe that public cloud is the future for most organizations and this is why I specialize in public clouds (Amazon Web Services and Azure) and hybrid cloud strategy. My unique role at Rackspace is to guide our customers in their cloud strategy and ensure that their strategy is aligned with their business organisation.
I started my career equally a developer and accept connected programming and scripting as a hobby. This is the reason why I am a large proponent of DevOps. I believe PowerShell is a fantastic tool that facilitates the procedure of joining the Dev and Ops worlds.
Contact information:
- Twitter: @rudolfvesely
- Blog: Technology Stronghold
Introduction
Many new features in Windows Server 2016 (in whatsoever Technical Preview) volition describe your attention, and it'due south very easy to miss some of them. This is truthful especially when people don't speak or blog about them too much like they practice for Windows PowerShell five.0, Storage Spaces Direct, or Storage Replica, as examples.
One characteristic that drew my attention is a new feature in Hyper-5 called detached device assignment. Information technology can be very just described as a device laissez passer-through feature, the likes of which has existed on other hypervisors for many years.
Microsoft started with device pass-through on Hyper-V with deejay pass-through (attaching a concrete disk without using VHD / VHDX), simply true pass-through came with single root I/O virtualization (SR-IOV) on Windows Server 2012. I recommend that you read John Howard'southward splendid weblog postal service serial that describes SR-IOV and hardware and system requirements.
On Windows Server 2016, nosotros finally go the ability to straight piece of work with devices on the host and attach them to a kid partition (guest VM) without being limited to merely networking and storage. This feature was probably built for passing-through graphics processing units (GPUs) in Azure for Due north-series VMs (GPU-enabled VMs), but we can utilize it for anything else. Please keep in listen that this is at your own risk. Microsoft will not support your setups, and you may also take very hard security bug. Any device pass-through on any hypervisor opens the possibility to accept down the host (for case, past triggering an fault on the PCI Limited passenger vehicle) or worse, taking control of your host.
The final thing you need to consider is whether you have hardware to examination on it. You need a mod customer computer or server that has Intel Virtualization Technology for Directed I/O (VT-d) or AMD Virtualization (AMD-5). I utilize an industrial mini PC, which volition be my new router and wireless access point (all virtualized), but you should be fine with a mod laptop. Then, if you're still reading, activate Intel VT-d in firmware of your testing computer, install the latest Technical Preview of Windows Server 2016, and beginning with PnpDevice.
PnpDevice module
On Windows Server 2016, thank you to the PnpDevice module, we finally take the possibility to work with hardware without directly touching Windows Management Instrumentation (WMI). The PnpDevice module will be very important for Nano Server and not-GUI servers, so I recommend that y'all endeavor it.
Get-Command -Module PnpDevice
CommandType Proper name Version Source
----------- ---- ------- ------
Office Disable-PnpDevice one.0.0.0 PnpDevice Role Enable-PnpDevice 1.0.0.0 PnpDevice Part Get-PnpDevice 1.0.0.0 PnpDevice Function Get-PnpDeviceProperty 1.0.0.0 PnpDevice
Let's have a expect what is attached to your organization by using:
Get-PnpDevice –PresentOnly | Sort-Object –Belongings Grade
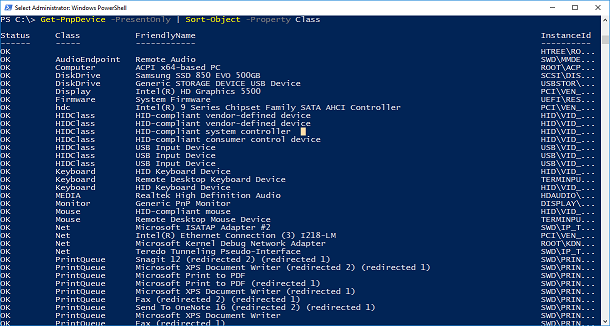
A lot of devices were returned. Now it's a good idea to choose what should be passed. I do not have multiple GPUs to pass it, just my goal is to virtualize my router and access point, and I have two wireless adapters in mini PCI-e slots. I found that the easiest way to find them is by using vendor ID:
(Get-PnpDevice -PresentOnly).Where{ $_.InstanceId -like '*VEN_168C*' } # 168C == Qualcomm Atheros
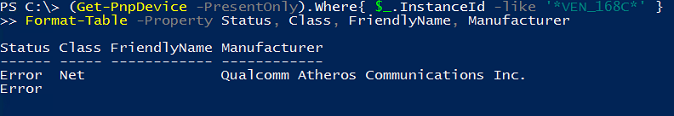
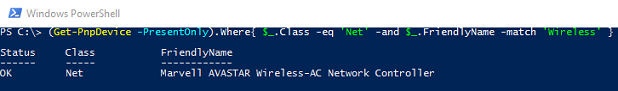
If you installed drivers on your host for devices that yous want to pass through (I did not), you lot can filter according to Form Net like this (case from my Surface Book):
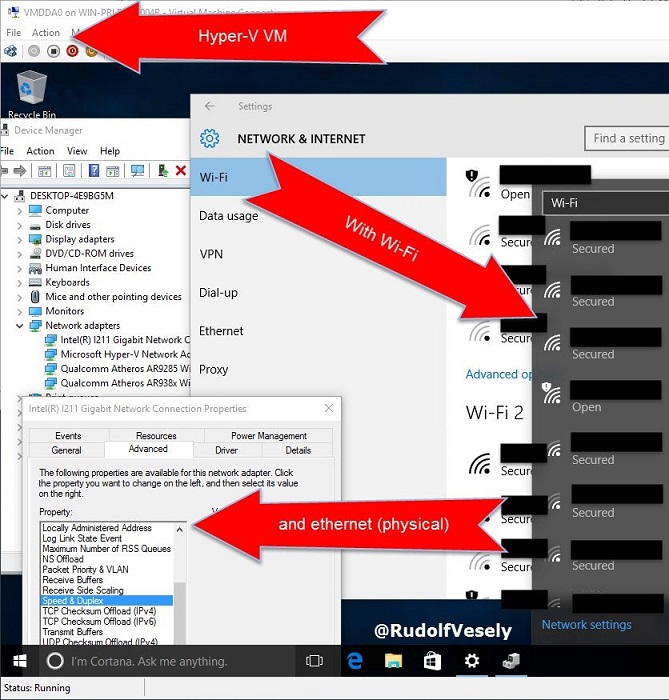
I will assume that you have installed the VM and chosen a device to adhere to it. I installed Windows x version 1511 considering this is the easiest method to test that dual dynamic acceleration (DDA) works. Later on I will endeavor replacing Windows with virtualized pfSense (FreeBSD appliance) and DD-WRT (Linux appliance). Especially in FreeBSD, I might take problems with drivers, and I am sure that I volition accept no issues with drivers in Windows 10.
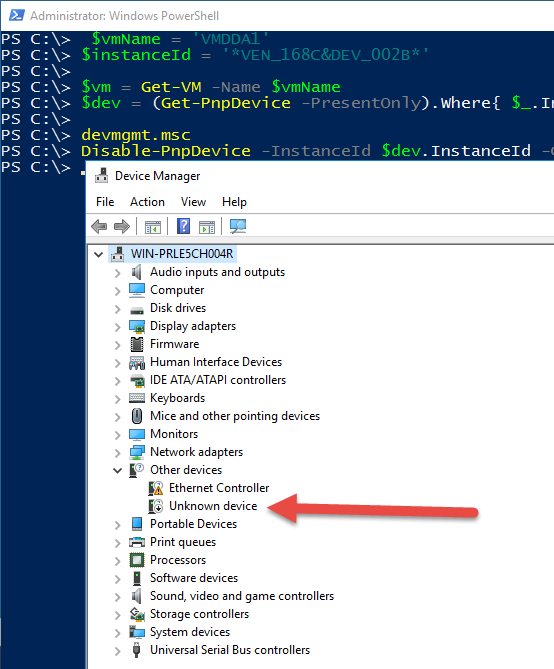
Permit'southward get VM object and device object of my Wi-Fi adapter:
$vmName = 'VMDDA1' $instanceId = '*VEN_168C&DEV_002B*'
$vm = Become-VM -Proper name $vmName $dev = (Get-PnpDevice -PresentOnly).Where{ $_.InstanceId -like $instanceId }
Our outset action should exist to disable the device. Y'all can bank check Device Manager past typing devmgmt.msc in the PowerShell console to see that the right device was disabled.
# Make certain that your console or integrated scripting environment (ISE) runs in elevated manner Disable-PnpDevice -InstanceId $dev.InstanceId -Confirm:$simulated
Mount
Now nosotros need to dismount the device from the host past using the Dismount-VmHostAssignableDevice cmdlet. To specify a location of the device, nosotros need to become a specific property that is not presented in the device object past using Become-PnpDeviceProperty.
locationPath = (Become-PnpDeviceProperty -KeyName DEVPKEY_Device_LocationPaths -InstanceId $dev.InstanceId).Data[0] Dismount-VmHostAssignableDevice -LocationPath $locationPath -Force –Verbose
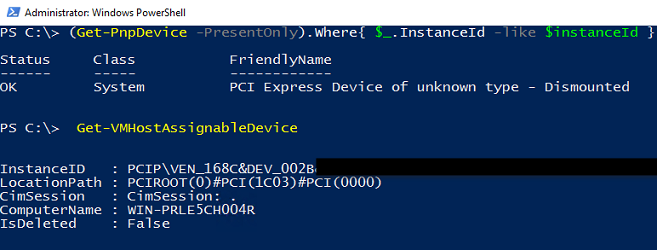
Now if you refresh the device object, you can see that something changed: Device is described as "Dismounted":
(Become-PnpDevice -PresentOnly).Where{ $_.InstanceId -like $instanceId }
You can cheque available assignable devices by using Get-VMHostAssignableDevice:
The last stride is to attach an assignable device to the VM by using Add-VMAssignableDevice similar this:
Add-VMAssignableDevice -VM $vm -LocationPath $locationPath –Verbose
You may go error similar this one:
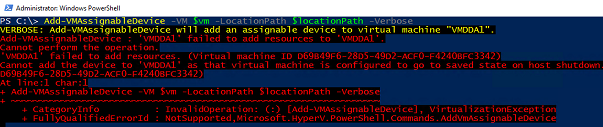
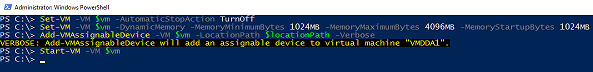
This is considering y'all haven't modified the VM configuration after you created information technology. In that location are two main requirements for passing through. The first is that the VM has to have Automatic Stop Action prepare to Turn off the virtual machine. This will probably be the merely VM on your host that has this configuration because nosotros usually want Close down or Salve. The second requirement is memory configuration. Dynamic memory is allowed, simply minimum and startup memory have to be equal. Allow'south set up it, and finally attach our device.
Set-VM -VM $vm -DynamicMemory -MemoryMinimumBytes 1024MB -MemoryMaximumBytes 4096MB -MemoryStartupBytes 1024MB -AutomaticStopAction TurnOff Add-VMAssignableDevice -VM $vm -LocationPath $locationPath –Verbose
If you spend some time playing with DDA, you can terminate, for example, with multiple Wi-Fi adapters and i physical like I did (all functional):
Restore configuration
That was fun! At present it's time to render devices to the host.
# Remove all devices from a single VM Remove-VMAssignableDevice -VMName VMDDA0 -Verbose
# Render all to host Go-VMHostAssignableDevice | Mount-VmHostAssignableDevice -Verbose
# Enable it in devmgmt.msc (Get-PnpDevice -PresentOnly).Where{ $_.InstanceId -friction match 'VEN_168C&DEV_002B' } | Enable-PnpDevice -Confirm:$fake -Verbose
Total code
$vmName = 'VMDDA0' $instanceId = '*VEN_168C&DEV_002B*' $ErrorActionPreference = 'Stop' $vm = Become-VM -Name $vmName $dev = (Go-PnpDevice -PresentOnly).Where{ $_.InstanceId -similar $instanceId } if (@($dev).Count -eq 1) {
Disable-PnpDevice -InstanceId $dev.InstanceId -Ostend:$fake $locationPath = (Get-PnpDeviceProperty -KeyName DEVPKEY_Device_LocationPaths -InstanceId $dev.InstanceId).Data[0] Dismount-VmHostAssignableDevice -LocationPath $locationPath -Force -Verbose Set up-VM -VM $vm -DynamicMemory -MemoryMinimumBytes 1024MB -MemoryMaximumBytes 4096MB -MemoryStartupBytes 1024MB -AutomaticStopAction TurnOff
# If y'all want to play with GPUs: # Gear up-VM -VM $vm -StaticMemory -MemoryStartupBytes 4096MB -AutomaticStopAction TurnOff # Set up-VM -VM $vm -GuestControlledCacheTypes $true -LowMemoryMappedIoSpace 2048MB -HighMemoryMappedIoSpace 4096MB -Verbose
Add-VMAssignableDevice -VM $vm -LocationPath $locationPath -Verbose
} else {
$dev | Sort-Object -Property Grade | Format-Tabular array -AutoSize Write-Mistake -Bulletin ('Number of devices: {0}' -f @($dev).Count)
Thanks for reading, and see y'all in the next article.
Rudolf
Thanks, Rudolf, for sharing your fourth dimension and knowledge.
I invite you to follow me on Twitter and Facebook. If you have any questions, send email to me at scripter@microsoft.com, or post your questions on the Official Scripting Guys Forum. Too check out my Microsoft Operations Management Suite Blog. See you tomorrow. Until then, peace.
Ed Wilson, Microsoft Scripting Guy
Source: https://devblogs.microsoft.com/scripting/passing-through-devices-to-hyper-v-vms-by-using-discrete-device-assignment/
0 Response to "How to Read a Pnpdevice as an Object Powershell"
Post a Comment